The online world is a Wild West when it comes to security. You can’t believe everything you see on the internet, because there are plenty of malicious folks who want nothing more than to rip you off.
One of the most popular types of online scams comes in the form of fake tech support. A con artist falsely claims that your computer has a lot of issues and “proves” it to you so you open up your wallet. Let’s take a look at how these tech support scams develop, so you can educate your employees to spot these fraudulent circumstances before they cost your business.
The Initial Bait
Typically, tech support scams arise in two ways. Sometimes, the swindler will cold-call you by phone and claim that he works for Microsoft. They usually explain that they’ve noticed some viruses on your computer, and that he wants to help you clean them up.
Of course, this is completely bogus. It’s important to remember that Microsoft and other reputable companies will never contact you out of the blue like this. HP, Lenovo, Microsoft, and others are not actively monitoring your computer for malware, nor do they have the capability to do so. If someone contacts you and claims to work for one of these companies, just hang up.
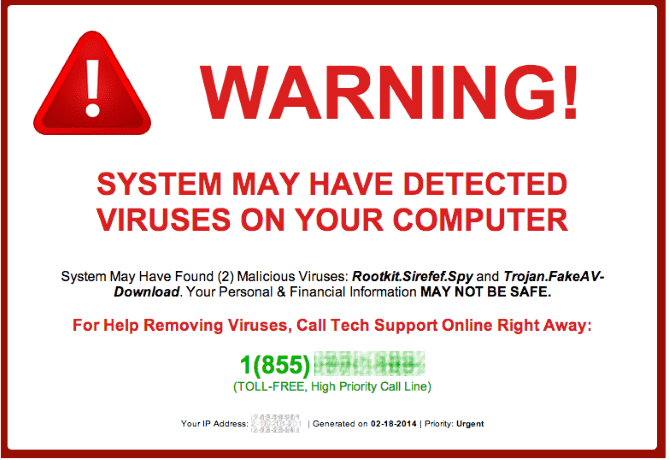
The other method of attack is via internet advertisements. Typically these ads are exaggerated and easy to ignore, but novice users might have trouble distinguishing real alerts with fake ones.
Once the user sees a malicious ad letting them know their computer needs help, they call a number and get connected to the scammer.
Gaining Access
If the victim seems to believe the scammer, their next step is to gain remote access to the victim’s PC. Typically, they’ll ask the user to download TeamViewer or another free remote desktop tool so that “Microsoft” can help remove their viruses.
TeamViewer is a useful and legitimate product, but those with evil intent can use it just as easily as those trying to help. You should never initiate a remote desktop session with someone you don’t trust.
Proving Their Case
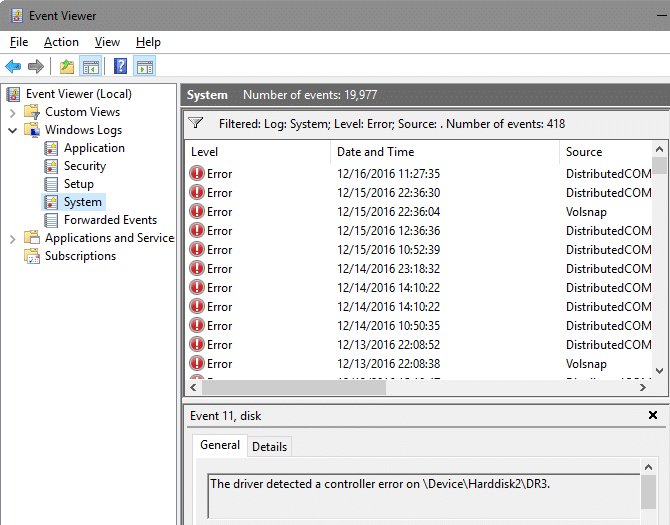
Now that the scammer has remote access, they want to “prove” that your computer is full of viruses. To accomplish this, they typically show the victim the Windows Event Viewer or other utilities designed for IT professionals to diagnose issues.
This utility contains hundreds of “errors,” which look scary to the average user but aren’t of any real concern. Windows collects small problems here, like failure to load a program at startup or the clock being off by a half second. Now, the frightened user wants the scammer’s help to remove the “infection.”
The Damage Done
The friendly person on the phone wants to help, but they aren’t doing this for charity! Before proceeding, they’ll need your credit card information so they can provide you with a powerful PC cleaner that will remove the viruses.
That’s their story, but of course they aren’t doing anything more than ripping you off here. They’ll ask for some money for a bogus antivirus product that doesn’t do anything. Their actions at this point vary — some will clear out the Event Viewer to make it look like the “viruses” are gone, while others will run once they’ve got your credit card info.
It’s worth repeating: if someone asks for your credit card information on a phone call you didn’t initiate, you should not give it to them!
Beating Tech Support Scams
These scammers like to prey on those whose job is not IT. This tactic clearly works, as these scams are still circulating after several years.
So, if you ever receive a call from someone claiming to be from Microsoft to help you with your computer, just hang up. Don’t entertain the call, and certainly never provide remote access to your machine to some random person on the phone. If you ever think you have a virus, get in contact with your local IT support staff and they’ll help you out!
Have you ever been contacted by a tech support scammer? Leave a comment with your story if so!
Image credit: Malwarebytes.org